- Common Scrambling Algorithm
-
The Common Scrambling Algorithm (or CSA) is the encryption algorithm used in the DVB digital television broadcasting for encrypting video streams.
CSA was specified by ETSI and adopted by the DVB consortium in May 1994.
Contents
History
CSA was largely kept secret until 2002. The patent papers gave some hints, but important details, like the layout of the so-called S-boxes, remained secret. Without these free implementations of the algorithm were out of question. Initially, CSA was to remain implemented in hardware only, and this would have made it difficult to reverse engineer existing implementations.
In 2002 FreeDec was released, implementing CSA in software. Though released as binary only, disassembly revealed the missing details and allowed reimplementation of the algorithm in higher-level programming languages.
With CSA now publicly known in its entirety, cryptanalysts started looking for weaknesses.
Description of the cipher
The CSA algorithm is composed of two distinct ciphers: a block cipher and a stream cipher.
When used in encryption mode the data are first encrypted using the 64 bits block cipher in CBC mode, starting from packet end. The stream cipher is then applied from packet start.
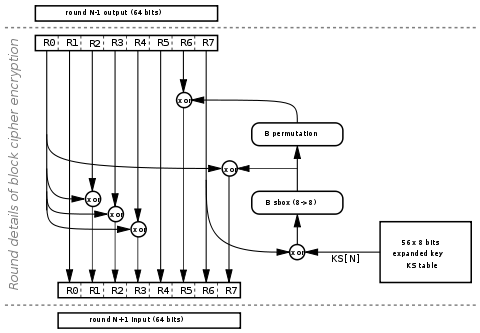
Block cipher
The block cipher process 64 bits blocks in 56 rounds. It uses 1 byte from expanded key on each round.
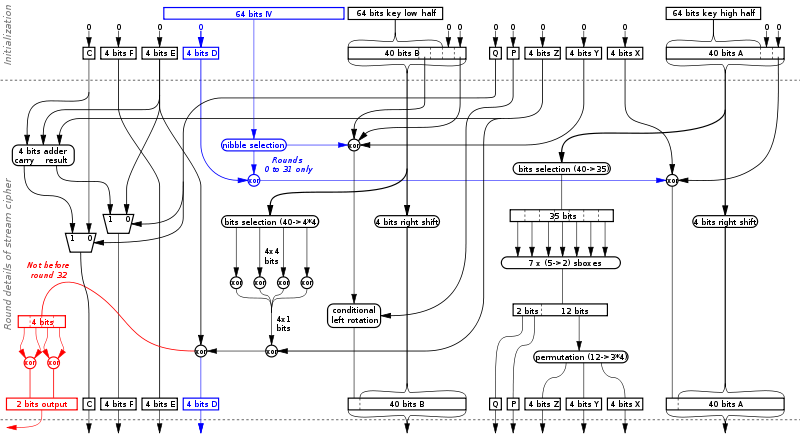
Stream cipher
The first 32 round of the stream cipher are used for initialization and do not generate any output. The first 64 bits of data are used as initialization vector during this phase and are left unchanged. The stream cipher then generates 2 bits of pseudo-random stream on each round which are xored starting at bit 64 of the packet.
Weaknesses
Were CSA to be broken, encrypted DVB transmissions would be decipherable, regardless of any proprietary conditional access (CA) system used. This could seriously compromise paid digital television services, as DVB has been standardised on for digital terrestrial television in Europe and elsewhere, and is used by many satellite television providers. No attack has yet been published, however.
Cryptanalysis
Like other encryption algorithms, a weak spot arises inasmuch that parts of the message are known or at least easily predictable, like MPEG headers. The length of the key is 64 bits, which allows for many different possibilities of encryption. A brute force attack taking 1 μs for each try, through all possible key words, would take around 300,000 years, on average. This could be reduced by using the predictable parts of the encrypted message to rule out potential keys, however this would require cryptanalysis of both stream cipher and block cipher algorithms at the same time which is a complicated task.
Brute force approach
While CSA algorithm uses 64-bit keys, most of the time only 48 bits of key are unknown, since bytes 3 and 7 are used as checksum bytes in CA systems, and may be easily recalculated. This allow reducing the brute force search time.
Theoretical implementation in a FPGA that would consist of 42 hw-threads that each would test 1 key per clock-cycle. At a clock-rate of 50Mhz this would allow the key to be found in ~19 days since we would expect, on average, to find the key after 247 tries for a 248 key. The problematic part in this would be to determine when a valid key was found since that would involve checking the decrypted data for known things like MPEG-headers which could be hard to implement efficiently enough to fit in a today commercially available FPGA. One possible way to reduce the needed complexity in the FPGA could be to have a multi-layer approach where the first one just discards all keys that are known to be invalid with quite simple checks and one or more that checks for additional information.
Most CA systems use short lived keys which are replaced every few seconds, making such implementation useless until computational power increase dramatically. Moreover, the usual 48 bits key length may still be increased to 64 bits in the future to improve system strength, as this is not a limitation of the algorithm.
References
- Wirt, Kai (November 2003). "Fault attack on the DVB Common Scrambling Algorithm (Report 2004/289)". Cryptology ePrint Archive. http://eprint.iacr.org/2004/289/.
External links
- Analysis of the DVB Common Scrambling Algorithm
- libdvbcsa: A free implementation of the DVB Common Scrambling Algorithm
- Improved Cryptanalysis of the Common Scrambling Algorithm Stream Cipher
- ETSI.org DVB CSA systems
Conditional access DVB Smart cards and encryption BISS · Conax · Cryptoworks · Digicipher · Irdeto · KeyFly · Nagravision · NDS · VideoGuard · PowerVu · RAS · SECA Mediaguard · Viaccess · WegenerDigital video disc DRM Data security Analogue broadcast encoding See also free to view and pay televisionCategories:- Cryptographic algorithms
- DVB
Wikimedia Foundation. 2010.