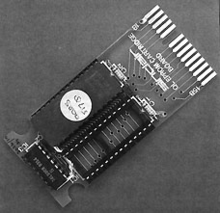
- Software protection dongle
-
This article is about the software protection devices. "Dongle" can also refer to, e.g., serial ports, USB flash drives, wireless networking devices, USB Mobile broadband modems.
A software protection dongle is a small piece of hardware that plugs into an electrical connector on a laptop, desktop or server computer. The term "dongle" was originally used to refer only to software-protection dongles; however, currently "dongle" is often used to refer to any small piece of hardware that plugs into a computer. This article is limited in scope to dongles used for the purpose of copy protection or authentication of software to be used on that system.[1]
Electrically, dongles mostly appear as two-interface security tokens with transient data flow that does not interfere with other dongle functions and a pull communication that reads security data from the dongle. These are used by some proprietary vendors as a form of copy protection or digital rights management, because it is generally harder to replicate a dongle than to copy the software it authenticates. Without the dongle, the software may run only in a restricted mode, or not at all. As of July 26, 2010 it is legal in the United States to use programs protected by this method without a dongle, if the dongle is no longer working and a replacement not available.[2]
Contents
History
In 1980, WORDCRAFT became one of the earliest programs to use a software protection dongle.[citation needed] Its dongle was a simple passive device that supplied data to the pins of a Commodore PET's external cassette port in a predetermined manner. This was possible because the PET cassette port supplied both power and data connections through a proprietary edge connector. It did, however, make the cassette port unusable for its intended purpose.
The two-cubic-inch (32 cm³) resin-potted first generation device was called a "dongle" by the inventor, in the absence of a suitable term. The distributor, Dataview Ltd., then based in Colchester, UK, then went on to produce a derivative dongle, which became their core business.
An early example of the term was in 1984, when early production Sinclair QLs were shipped with part of the QL firmware held on an external 16 KB ROM cartridge (infamously known as the "kludge" or "dongle"), until the QL was redesigned to increase the internal ROM capacity from 32 to 48 KB.[3][4]
Dongles rapidly evolved into active devices that contained a serial transceiver (UART) and even a microprocessor to handle transactions with the host. Later versions adopted the USB interface in preference to the serial or parallel interface. The USB interface is gradually becoming dominant.
A 1992 advertisement for Rainbow Technologies claimed the word dongle was derived from the name "Don Gall". Though untrue, this has given rise to an urban myth.[5]
The Monty Python's Flying Circus episode It's the arts contains the pseudo-German proper noun fragment dingle- dangle- dongle [6] and it's possible the physical dangling out of the device inspired the consonant name.
Copy protection
 USB dongles in two case sizes
USB dongles in two case sizes
Vendors of software-protection dongles (and dongle-controlled software) often use terms such as "hardware key", "hardware token", or "security device" instead of "dongle", but the term "dongle" is much more common in day-to-day use.citation needed
Usage
Efforts to introduce dongle copy-protection in the mainstream software market have met stiff resistance from users. Such copy-protection is more typically used with very expensive packages and vertical market software, such as CAD/CAM software, MICROS Systems hospitality and special retail software, Digital Audio Workstation applications, and some translation memory packages. The vast majority of printing and prepress software, such as CtP workflows, require dongles.
In cases such as prepress and printing software, the dongle is encoded with a specific, per-user license key, which enables particular features in the target application. This is a form of tightly controlled licensing, which allows the vendor to engage in vendor lock-in and charge more than it would otherwise for the product. An example is the way Kodak licenses Prinergy to customers: When a computer-to-plate output device is sold to a customer, Prinergy's own license cost is provided separately to the customer, and the base price contains little more than the required licenses to output work to the device. USB dongles are also a big part of Steinberg's audio production and editing systems, such as Cubase, Wavelab, Hypersonic, HALion, and others. The dongle used by Steinberg's products is also known as a Steinberg Key. The Steinberg Key can be purchased separately from its counterpart applications and generally comes bundled with the "Syncrosoft License Control Center" application, which is cross-platform compatible with both Mac OS X and Windows.
Some software developers use traditional USB flash drives as software license dongles that contain hardware serial numbers in conjunction with the stored device ID strings, which are generally not easily changed by an end-user. A developer can also use the dongle to store user settings or even a complete "portable" version of the application. Not all flash drives are suitable for this use, as not all manufacturers install unique serial numbers into their devices. Although such medium security may deter a casual hacker, the lack of a processor core in the dongle to authenticate data, do encryption/decryption, and execute inaccessible binary code makes such a passive dongle inappropriate for all but the lowest-priced software. A simpler and even less secure option is to use unpartitioned or unallocated storage in the dongle to store license data. Common USB flash drives are relatively inexpensive compared to dedicated security dongle devices, but reading and storing data in a flash drive are easy to intercept, alter, and bypass.
Issues
There are potential weaknesses in the implementation of the protocol between the dongle and the copy-controlled software. It requires considerable cunning to make this hard to crack. For example, a simple implementation might define a function to check for the dongle's presence, returning "true" or "false" accordingly, but the dongle requirement can be easily circumvented by modifying the software to always answer "true".
Modern dongles include built-in strong encryption and use fabrication techniques designed to thwart reverse engineering. Typical dongles also now contain non-volatile memory — key parts of the software may actually be stored and executed on the dongle. Thus dongles have become secure cryptoprocessors that execute inaccessible program instructions that may be input to the cryptoprocessor only in encrypted form. The original secure cryptoprocessor was designed for copy protection of personal computer software (see US Patent 4,168,396, Sept 18, 1979)[7] to provide more security than dongles could then provide. See also bus encryption.
In counterfeit versions of a program, the code to check for a dongle is often deleted or circumvented. As a result, the counterfeit version may be easier to use and thus may be preferable to the original.
Hardware cloning, where the dongle is emulated by a device driver, is also a threat to traditional dongles. To thwart this, some dongle vendors adopted smart card product, which is widely used in extremely rigid security requirement environments such as military and banking, in their dongle products.
Dongle drivers bring problems for end-users. Most developers and software vendors want to get rid of the dongle driver headache. There are some driverless dongles on the market, which make the protection easy for both software vendors and end-users. Most of driverless dongles are based-on HID technology, which is working like a mouse or keyboard.
A more innovative modern dongle is designed with a code porting mechanism, meaning you can transfer part of your important program code or license enforcement into a secure hardware environment (such as in a smart card OS, mentioned above). An ISV can port thousands of lines of important computer program code into the dongle.
The real-time dongle contains an internal real-time clock, independent from the Operating system clock, and designed for software vendors who need to control and manage rental and sale usage and/or maintenance. This allows pay per use by charging the end users timely and periodically for actual periods of use. This function is based on a real-time clock in the dongle which records the specific time (hour, minute, second) and date (day, month, year). If there isn't a battery inside the dongle, it is not a real-time dongle. There are only three real-time dongles: CodeMeter CmStick/T, HASP Time and UniKey Time.
Game consoles
Some unlicensed titles for game consoles used dongles to connect to officially licensed cartridges, in order to circumvent the authentication chip embedded in the console.
With the Nintendo DS and the Nintendo DS Lite having a slot that can accommodate Game Boy Advance games, a few DS games have used this GBA slot to allow interaction between DS games and GBA games while both are plugged in. Since in this case the DS game is running and the GBA game is simply serving in a read-only capacity (the player may sometimes use data from the GBA game, but cannot actively play it in this mode), many people refer to the GBA game plugged in as the "dongle" game. This is notably used in the popular Pokémon Diamond and Pearl, Pokémon Platinum, and Pokémon HeartGold and SoulSilver games. The Nintendo DSi does not have a GBA game slot, which means it cannot be used in the same way as the original DS or the DS Lite, a decision that was highly controversial.
Hardware issues
Older dongles are built for parallel interfaces. Some newer computers and especially notebooks do not have these interfaces, so the software is not usable on these devices without expansion cards, and sometimes even with them (if it checks IRQ ports).
Another issue with dongles is that they can be lost, damaged or stolen. Without a dongle, a software package is typically rendered useless until a replacement key or package is purchased. However, it is a common practice for a software company to charge the full price of a brand new package to replace the software dongle.
Manufacturers
- SafeNet Inc. – Aladdin[8] – Hardlock, HASP, Sentinel
- SecuTech Solution Inc. [9] – UniKey
- Wibu-Systems [10] – CodeMeter, WibuKey
- MicroWorks, Inc. [11] – SmartDongle
- MARX CrypoTech LP[12] – MARX CRYPTO-BOX USB dongles for software and digital media protection.
- TDi GmbH[13] – Matrix dongles
See also
- License manager
- Product activation
- Digital rights management
- Trusted client
- Security token
- Lock-out chip
References
- ^ According to the Oxford English Dictionary, the first printed reference is from a Jan 1982 MicroComputer Printout Vol 2:19, "The word ‘dongle’ has been appearing in many articles with reference to security systems for computer software." (refers to alleged coinage in 1980)
- ^ http://www.gamepolitics.com/2010/07/26/us-govt-okays-jailbreaking-and-breaking-game-drm-investigative-purposes
- ^ Ian Adamson; Richard Kennedy. "The Quantum Leap – to where?". Sinclair and the 'Sunrise' Technology. http://www.nvg.ntnu.no/sinclair/computers/ql/ql_sst.htm. Retrieved 2006-12-15.
- ^ Rick Dickinson (2007-07-16). "QL and Beyond". Flickr. http://www.flickr.com/photos/9574086@N02/sets/72157600854938578/. Retrieved 2008-04-21.
- ^ See advertisement in Byte Magazine, August 1992, p. 133
- ^ "Episode Six". http://www.ibras.dk/montypython/episode06.htm. "Oh ja. When I first met Johann Gambolputty de von Ausfern- schplenden- schlitter- crasscrenbon- fried- digger- dingle- dangle- dongle- dungle-"
- ^ US Patent 4,168,396
- ^ During 2008 to 2009, due to the financial crisis, some mergers occurred among dongle manufacturers. Aladdin first bought Eutron, a European dongle vendor before 2008. Six months later, Aladdin was acquired by SafeNet. After this transaction, Rainbow (SafeNet), Aladdin (HASP) and Eutron merged to a single entity, SafeNet.[citation needed]
- ^ SecuTech is a vendor for driverless dongles, which are based on HID technologies.
- ^ Wibu-Systems lets frequently test the security of their products with a Hacker's Contest, see MacTech magazine: CodeMeter not cracked at international Hacker's Contest
- ^ MicroWorks is a vendor that provides open source for the APIs used to communicate with the SmartDongle.
- ^ MARX CRYPTO-BOX USB dongles for software and digital media protection
- ^ TDi GmbH is a vendor for driverless dongles. Beside software you can also protect excel files very easily.
External links
Categories:
Wikimedia Foundation. 2010.