- Cyberterrorism
-
Not to be confused with Internet and terrorism.
Cyberterrorism is the use of Internet based attacks in terrorist activities, including acts of deliberate, large-scale disruption of computer networks, especially of personal computers attached to the Internet, by the means of tools such as computer viruses.
Cyberterrorism is a controversial term. Some authors choose a very narrow definition, relating to deployments, by known terrorist organizations, of disruption attacks against information systems for the primary purpose of creating alarm and panic. By this narrow definition, it is difficult to identify any instances of cyberterrorism.
There is much concern from government and media sources about potential damages that could be caused by cyberterrorism, and this has prompted official responses from government agencies.
Several minor incidents of cyberterrorism have been documented.
Contents
Definition
There is debate over the basic definition of the scope of cyberterrorism. There is variation in qualification by motivation, targets, methods, and centrality of computer use in the act. Depending on context, cyberterrorism may overlap considerably with cybercrime or ordinary terrorism.[1]
Narrow definition
If cyberterrorism is treated similarly to traditional terrorism, then it only includes attacks that threaten property or lives, and can be defined as the leveraging of a target's computers and information, particularly via the Internet, to cause physical, real-world harm or severe disruption of infrastructure.
There are some[who?] who say that cyberterrorism does not exist and is really a matter of hacking or information warfare. They disagree with labeling it terrorism because of the unlikelihood of the creation of fear, significant physical harm, or death in a population using electronic means, considering current attack and protective technologies.
If a strict definition is assumed, then there have been no or almost no identifiable incidents of cyberterrorism, although there has been much public concern.
Broad definition
Cyberterrorism is defined by the Technolytics Institute as "The premeditated use of disruptive activities, or the threat thereof, against computers and/or networks, with the intention to cause harm or further social, ideological, religious, political or similar objectives. Or to intimidate any person in furtherance of such objectives." [2] The term was coined by Barry C. Collin.[3]
The National Conference of State Legislatures, an organization of legislators created to help policymakers issues such as economy and homeland security defines cyberterrorism as:
[T]he use of information technology by terrorist groups and individuals to further their agenda. This can include use of information technology to organize and execute attacks against networks, computer systems and telecommunications infrastructures, or for exchanging information or making threats electronically. Examples are hacking into computer systems, introducing viruses to vulnerable networks, web site defacing, Denial-of-service attacks, or terroristic threats made via electronic communication.[4]
For the use of the Internet by terrorist groups for organization, see Internet and terrorism.
Cyberterrorism can also include attacks on Internet business, but when this is done for economic motivations rather than ideological, it is typically regarded as cybercrime.
As shown above, there are multiple definitions of cyber terrorism and most are overly broad. There is controversy concerning overuse of the term and hyperbole in the media and by security vendors trying to sell "solutions".[5]
Concerns
As the Internet becomes more pervasive in all areas of human endeavor, individuals or groups can use the anonymity afforded by cyberspace to threaten citizens, specific groups (i.e. with membership based on ethnicity or belief), communities and entire countries, without the inherent threat of capture, injury, or death to the attacker that being physically present would bring.
As the Internet continues to expand, and computer systems continue to be assigned more responsibility while becoming more and more complex and interdependent, sabotage or terrorism via cyberspace may become a more serious threat and is possibly one of the top 10 events to "end the human race".[6]
History
Public interest in cyberterrorism began in the late 1980s. As 2000 approached, the fear and uncertainty about the millennium bug heightened and interest in potential cyberterrorist attacks also increased. However, although the millennium bug was by no means a terrorist attack or plot against the world or the United States, it did act as a catalyst in sparking the fears of a possibly large-scale devastating cyber-attack. Commentators noted that many of the facts of such incidents seemed to change, often with exaggerated media reports.
The high profile terrorist attacks in the United States on September 11, 2001 and the ensuing War on Terror by the US led to further media coverage of the potential threats of cyberterrorism in the years following. Mainstream media coverage often discusses the possibility of a large attack making use of computer networks to sabotage critical infrastructures with the aim of putting human lives in jeopardy or causing disruption on a national scale either directly or by disruption of the national economy.
Authors such as Winn Schwartau and John Arquilla are reported to have had considerable financial success selling books which described what were purported to be plausible scenarios of mayhem caused by cyberterrorism. Many critics claim that these books were unrealistic in their assessments of whether the attacks described (such as nuclear meltdowns and chemical plant explosions) were possible. A common thread throughout what critics perceive as cyberterror-hype is that of non-falsifiability; that is, when the predicted disasters fail to occur, it only goes to show how lucky we've been so far, rather than impugning the theory.
International responses
U.S. military
The US Department of Defense (DoD) charged the United States Strategic Command with the duty of combating cyberterrorism. This is accomplished through the Joint Task Force-Global Network Operations, which is the operational component supporting USSTRATCOM in defense of the DoD's Global Information Grid. This is done by integrating GNO capabilities into the operations of all DoD computers, networks, and systems used by DoD combatant commands, services and agencies.
On November 2, 2006, the Secretary of the Air Force announced the creation of the Air Force's newest MAJCOM, the Air Force Cyber Command, which would be tasked to monitor and defend American interest in cyberspace. The plan was however replaced by the creation of Twenty-Fourth Air Force which became active in August 2009 and would be a component of the planned United States Cyber Command.
On December 22, 2009, the White House named its head of Cyber Security as Howard Schmidt. He will coordinate U.S Government, military and intelligence efforts to repel hackers.
Israel
In May 2011 Israeli Prime Minister Benjamin Netanyahu announced the establishment of the National Internet Defense Taskforce, charged with developing tools to secure vital Israeli online infrastructure. "The main responsibility of the taskforce will be to expand the state's ability to defend vital infrastructure networks against cybernetic terrorist attacks perpetrated by foreign countries and terrorist elements," said a statement from the Prime Minister's Office.[7][8]
China
The Chinese Defense Ministry confirmed the existence of an online defense unit in May 2011. Composed of about thirty elite internet specialists, the so-called "Cyber Blue Team," or "Blue Army," is officially claimed to be engaged in cyber-defense operations, though there are fears the unit has been used to penetrate secure online systems of foreign governments.[9][10]
Examples
Sabotage
Mostly non-political acts of sabotage have caused financial and other damage, as in a case where a disgruntled employee caused the release of untreated sewage into water in Maroochy Shire, Australia.[11]
More recently, in May 2007 Estonia was subjected to a mass cyber-attack in the wake of the removal of a Russian World War II war memorial from downtown Tallinn. The attack was a distributed denial-of-service attack in which selected sites were bombarded with traffic to force them offline; nearly all Estonian government ministry networks as well as two major Estonian bank networks were knocked offline; in addition, the political party website of Estonia's current Prime Minister Andrus Ansip featured a counterfeit letter of apology from Ansip for removing the memorial statue. Despite speculation that the attack had been coordinated by the Russian government, Estonia's defense minister admitted he had no conclusive evidence linking cyber attacks to Russian authorities. Russia called accusations of its involvement "unfounded," and neither NATO nor European Commission experts were able to find any conclusive proof of official Russian government participation.[12] In January 2008 a man from Estonia was convicted for launching the attacks against the Estonian Reform Party website and fined.[13][14]
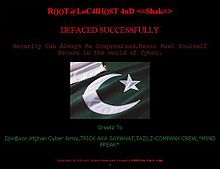
Website defacement and denial of service
Even more recently, in October 2007, the website of Ukrainian president Viktor Yushchenko was attacked by hackers. A radical Russian nationalist youth group, the Eurasian Youth Movement, claimed responsibility.[15]
In 1999 hackers attacked NATO computers. The computers flooded them with email and hit them with a denial of service (DoS). The hackers were protesting against the NATO bombings in Kosovo. Businesses, public organizations and academic institutions were bombarded with highly politicized emails containing viruses from other European countries.[16]
In fiction
- The Japanese cyberpunk manga, Ghost in the Shell (as well as its popular movie and TV adaptations) centers around an anti-cyberterrorism and cybercrime unit. In its mid-21st century Japan setting such attacks are made all the more threatening by an even more widespread use of technology including cybernetic enhancements to the human body allowing people themselves to be direct targets of cyberterrorist attacks.
- Dan Brown's Digital Fortress.
- Amy Eastlake's Private Lies.
- In the movie Live Free or Die Hard, John McClane (Bruce Willis) takes on a group of cyberterrorists intent on shutting down the entire computer network of the United States.
- The movie Eagle Eye involves a super computer controlling everything electrical and networked to accomplish the goal.
- The plots of 24 Day 4 and Day 7 include plans to breach the nation's nuclear plant grid and then to seize control of the entire critical infrastructure protocol.
- The Tom Clancy created series Netforce was about a FBI/Military team dedicated to combating cyberterrorists.
- Much of the plot of Mega Man Battle Network is centered around cyberterrorism.
- In the 2009 Japanese animated film Summer Wars, an artificial intelligence cyber-terrorist attempts to take control over the world's missiles in order to "win" against the main characters that attempted to keep it from manipulating the world's electronic devices.
See also
- Cyberwarfare
- Cyberbullying
- Cyber Operations
- Cyberstalking
- Internet and terrorism
- US-CERT (United States Computer Emergency Readiness Team)
- Patriot hacking
- 2007 cyberattacks on Estonia
- Cyberattacks during the 2008 South Ossetia war
References
- ^ What is cyberterrorism? Even experts can't agree. Harvard Law Record. Victoria Baranetsky. November 5, 2009.
- ^ http://oai.dtic.mil/oai/oai?&verb=getRecord&metadataPrefix=html&identifier=ADA439217
- ^ Afroz, Soobia (June 16, 2002). "Cyber terrorism — fact or fiction?". Dawn. http://www.dawn.com/weekly/dmag/archive/020616/dmag21.htm. Retrieved 2008-08-30.
- ^ Cyberterrorism National Conference of State Legislatures.
- ^ Anderson, Kent (October 13, 2010). "Virtual Hostage: Cyber terrorism and politically motivated computer crime". The Prague Post. http://praguepost.com/opinion/5996-virtual-hostage.html. Retrieved 2010-10-14.
- ^ "Top 10 events that may end the human race". Yahoo News. Wed Oct 27, 2010. http://ca.news.yahoo.com/s/yahoocanada/101027/canada/top10_events_that_may_end_the_human_race. Retrieved 2010-11-01.
- ^ Lappin, Yaakov (18 May 2011). "Prime minister announces new cyber defense taskforce". Jerusalem Post. http://www.jpost.com/Defense/Article.aspx?id=221116. Retrieved 19 May 2011. "A national cyber defense taskforce will be set up to defend Israel's vital infrastructure from Internet-based terror attacks, Prime Minister Binyamin Netanyahu said on Wednesday."
- ^ Williams, Dan (18 May 2011). "Eye on tech exports, Israel launches cyber command". Reuters (Jerusalem). http://www.reuters.com/article/2011/05/18/israel-security-cyber-idUSLDE74H0RE20110518. Retrieved 19 May 2011. "The 80-person team led by a retired general and unveiled by Prime Minister Benjamin Netanyahu follows similar initiatives in the West as a precaution against industrialised nations falling prey to paralysing sabotage of their online systems."
- ^ Yu, Eileen (27 May 2011). "China dispatches online army". ZDNet Asia. http://www.zdnetasia.com/china-dispatches-online-army-62300502.htm. Retrieved 3 June 2011. "Geng Yansheng, spokesperson for China's Defense Ministry, was quoted to say that the PLA set up the cyberwar unit, or 'cyber blue team', to support its military training and upgrade the army's Internet security defense."
- ^ "China Confirms Existence of Elite Cyber-Warfare Outfit the 'Blue Army'". Fox News. 26 May 2011. http://www.foxnews.com/scitech/2011/05/26/china-confirms-existence-blue-army-elite-cyber-warfare-outfit/. Retrieved 3 June 2011. "China set up a specialized online 'Blue Army' unit that it claims will protect the People's Liberation Army from outside attacks, prompting fears that the crack team was being used to infiltrate foreign governments' systems."
- ^ Hacker jailed for reverse sewage. The Register. October 31, 2001.
- ^ Estonia has no evidence of Kremlin involvement in cyber attacks
- ^ "Estonia fines man for 'cyber war'". BBC. 2008-01-25. http://news.bbc.co.uk/2/hi/technology/7208511.stm. Retrieved 2008-02-23.
- ^ Leyden, John (2008-01-24). "Estonia fines man for DDoS attacks". The Register. http://www.theregister.co.uk/2008/01/24/estonian_ddos_fine. Retrieved 2008-02-22
- ^ Russian nationalists claim responsibility for attack on Yushchenko's Web site International Herald Tribune
- ^ "Hackers attack U.S. government Web sites in protest of Chinese embassy bombing". CNN. http://www.cnn.com/TECH/computing/9905/10/hack.attack/. Retrieved 2010-04-30.
Further reading
- Alexander, Yonah Swetman, Michael S. (2001). Cyber Terrorism and Information Warfare: Threats and Responses. Transnational Publishers Inc.,U.S.. ISBN 1-57105-225-9.
- Colarik, Andrew M. (2006). Cyber Terrorism: Political and Economic Implications. Idea Group, U.S.. ISBN 1-59904-022-0.
- Verton, Dan (2003). Black Ice: The Invisible Threat of Cyber-terrorism. Osborne/McGraw-Hill, U.S.. ISBN 0-07-222787-7.
- Weimann, Gabriel (2006). Terror on the Internet: The New Arena, the New Challenges. United States Institute of Peace, U.S.. ISBN 1-929223-71-4.
- Blau, John (Nov 2004) "The battle against cyberterror" NetworkWorld. Retrieved Mar 20, 2005 from the World Wide Web: http://www.nwfusion.com/supp/2004/cybercrime/112904terror.html
- Gross, Grant (Nov 2003) "Cyberterrorist attack would be more sophisticated that past worms, expert says" ComputerWorld. Retrieved Mar 17, 2005 from the World Wide Web: http://www.computerworld.com/securitytopics/security/story/0,10801,86857,00.html
- Poulsen, Kevin (Aug 2004) "South Pole 'cyberterrorist' hack wasn't the first" SecurityFocus News. Retrieved Mar 17, 2005 from the World Wide Web: http://www.securityfocus.com/news/9356.
- Thevenet, Cédric (Nov 2005) "Cyberterrorisme, mythe ou réalité?". From the World Wide Web : http://www.terrorisme.net/pdf/2006_Thevenet.pdf
- U.S. Army Cyber Operations and Cyber Terrorism Handbook 1.02
- Jacqueline Ching (2010). Cyberterrorism. Rosen Pub Group. ISBN 1435885325.
External links
General
- What is Cyberterrorism? Even experts can't agree in the Harvard Law Record
- AIC Australian Institute of Criminology - Cyberterrorism
- CRS Report for Congress - Computer Attack and Cyber Terrorism - 17/10/03
- Statement for the Record of Louis J. Freeh, Director Federal Bureau of Investigation on Cybercrime - Mar 28, 2000
- Cyber-Terrorism: Propaganda or Probability?
- FBI Laboratory - Cyberterrorism: Fact or Fancy by Mark M. Pollitt
- How terrorists use the Internet ABC Australia interview with Professor Hsinchun Chen on the Dark Internet.
- Department of Defense Cyber Crime Center
- Documentary about Cyberterrorism (in Spanish)
- [1]
- [2]
- Cyber Terrorism by Internet Security Visionary Melih Abdulhayoglu
- Information Warfare
- Stefano Mele, 31 May 2010, Le esigenze americane in tema di cyber-terrorismo e cyberwarfare. Analisi strategica delle contromisure (Italian)
- Stefano Mele, 30 Sep 2010, Cyberwarfare and its damaging effects on citizens
RedShield Association- Cyber Defense
- Cyber Infrastructure Protection - Strategic Studies Institute
News
- Politically Motivated Computer Crime - Current news on political hacking
- MSNBC - Hacker plan: take down the Net - Mar 3, 2000
- BBC News - Cyber terrorism 'overhyped' - 14/03/03
- BBC News - US warns of al-Qaeda cyber threat - 01/12/06
- NDTV News - Terror in cyber space toughest to check - 09/12/08
- Wanabehuman - modern militant, counter-terror use of the Internet - 25/01/07
- Wanabehuman - approaches to understanding radicalization - 02/05/07
Categories:- Cyberwarfare
- Computer crimes
- Terrorism by method
Wikimedia Foundation. 2010.