- Man-in-the-middle attack
-
Not to be confused with Meet-in-the-middle attack.
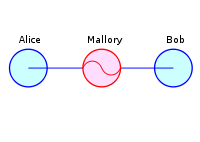
In cryptography, the man-in-the-middle attack (often abbreviated MITM), bucket-brigade attack, or sometimes Janus attack, is a form of active eavesdropping in which the attacker makes independent connections with the victims and relays messages between them, making them believe that they are talking directly to each other over a private connection, when in fact the entire conversation is controlled by the attacker. The attacker must be able to intercept all messages going between the two victims and inject new ones, which is straightforward in many circumstances (for example, an attacker within reception range of an unencrypted Wi-Fi wireless access point, can insert himself as a man-in-the-middle).
A man-in-the-middle attack can succeed only when the attacker can impersonate each endpoint to the satisfaction of the other—it is an attack on mutual authentication. Most cryptographic protocols include some form of endpoint authentication specifically to prevent MITM attacks. For example, SSL authenticates the server using a mutually trusted certification authority.
Contents
Need for additional transfer over a secure channel
With the exception of Interlock Protocol, all cryptographic systems that are secure against MITM attacks require an additional exchange or transmission of information over some kind of secure channel. Many key agreement methods have been developed, with different security requirements for the secure channel.
Example of an attack
Suppose Alice wishes to communicate with Bob. Meanwhile, Mallory wishes to intercept the conversation to eavesdrop and possibly deliver a false message to Bob .
First, Alice asks Bob for his public key. If Bob sends his public key to Alice, but Mallory is able to intercept it, a man-in-the-middle attack can begin. Mallory sends a forged message to Alice that claims to be from Bob, but instead includes Mallory's public key.
Alice, believing this public key to be Bob's, encrypts her message with Mallory's key and sends the enciphered message back to Bob. Mallory again intercepts, deciphers the message using her private key, possibly alters it if she wants, and re-enciphers it using the public key Bob originally sent to Alice. When Bob receives the newly enciphered message, he believes it came from Alice.
1. Alice sends a message to Bob, which is intercepted by Mallory:
Alice "Hi Bob, it's Alice. Give me your key"--> Mallory Bob
2. Mallory relays this message to Bob; Bob cannot tell it is not really from Alice:
Alice Mallory "Hi Bob, it's Alice. Give me your key"--> Bob
3. Bob responds with his encryption key:
Alice Mallory <--[Bob's_key] Bob
4. Mallory replaces Bob's key with her own, and relays this to Alice, claiming that it is Bob's key:
Alice <--[Mallory's_key] Mallory Bob
5. Alice encrypts a message with what she believes to be Bob's key, thinking that only Bob can read it:
Alice "Meet me at the bus stop!"[encrypted with Mallory's key]--> Mallory Bob
6. However, because it was actually encrypted with Mallory's key, Mallory can decrypt it, read it, modify it (if desired), re-encrypt with Bob's key, and forward it to Bob:
Alice Mallory "Meet me in the windowless van at 22nd Ave!"[encrypted with Bob's key]--> Bob
7. Bob thinks that this message is a secure communication from Alice.
This example shows the need for Alice and Bob to have some way to ensure that they are truly using each other's public keys, rather than the public key of an attacker. Otherwise, such attacks are generally possible, in principle, against any message sent using public-key technology. Fortunately, there are a variety of techniques that help defend against MITM attacks.
Defenses against the attack
Various defenses against MITM attacks use authentication techniques that are based on:
- Public key infrastructures
- Stronger mutual authentication, such as:
- Secret keys (which are usually high information entropy secrets, and thus more secure), or
- Passwords (which are usually low information entropy secrets, and thus less secure)
- Latency examination, such as with long Cryptographic hash function calculations that lead into tens of seconds; if both parties take 20 seconds normally, and the calculation takes 60 seconds to reach each party, this can indicate a third party
- Second (secure) channel verification
- One-time pads are immune to MITM attacks, assuming the security and trust of the one-time pad.
- Carry-forward verification
- Testing is being carried out on deleting compromised certificates from issuing authorities on the actual computers and compromised certificates are being exported to sandbox area before removal for analysis
The integrity of public keys must generally be assured in some manner, but need not be secret. Passwords and shared secret keys have the additional secrecy requirement. Public keys can be verified by a Certificate Authority, whose public key is distributed through a secure channel (for example, with a web browser or OS installation). Public keys can also be verified by a web of trust that distributes public keys through a secure channel (for example by face-to-face meetings).
See key-agreement protocol for a classification of protocols that use various forms of keys and passwords to prevent man-in-the-middle attacks.
Forensic analysis of MITM attacks
Captured network traffic from what is suspected to be a MITM attack can be analyzed in order to determine if it really was a MITM attack or not. Important evidence to analyze when doing network forensics of a suspected SSL MITM attack include:[1]
- IP address of the server
- DNS name of the server
- X.509 certificate of the server
- Is the certificate self signed?
- Is the certificate signed by a trusted CA?
- Has the certificate been revoked?
- Has the certificate been changed recently?
- Do other clients, elsewhere on the Internet, also get the same certificate?
Quantum cryptography
Quantum cryptography protocols typically authenticate part or all of their classical communication with an unconditionally secure authentication scheme (e.g. Wegman-Carter authentication).
Beyond cryptography
MITM should be seen as a general problem resulting from the presence of intermediate parties acting as proxy for clients on either side. If they are trustworthy and competent, all may be well; if they are not, nothing will be. How can one distinguish the cases? By acting as a proxy and appearing as the trusted client to each side, the intermediate attacker can carry out much mischief, including various attacks against the confidentiality or integrity of the data passing through it.
A notable non-cryptographic man-in-the-middle attack was perpetrated by one version of a Belkin wireless network router in 2003. Periodically, it would take over an HTTP connection being routed through it: this would fail to pass the traffic on to destination, but instead itself respond as the intended server. The reply it sent, in place of the web page the user had requested, was an advertisement for another Belkin product. After an outcry from technically-literate users, this 'feature' was removed from later versions of the router's firmware.[2]
Another example of a non-cryptographic man-in-the-middle attack is the "Turing porn farm." Brian Warner says this is a "conceivable attack" that spammers could use to defeat CAPTCHAs.[3] The spammer sets up a pornographic web site where access requires that the user solves the CAPTCHAs in question. However, Jeff Atwood points out that this attack is merely theoretical — there was no evidence by 2006 that any spammer had ever built a Turing porn farm.[4] However, as reported in an October, 2007 news story, spammers have indeed built a Windows game in which users type in CAPTCHAs acquired from the Yahoo webmail service, and are rewarded with pornographic pictures.[5] This allows the spammers to create temporary free email accounts with which to send out spam.
Implementations
- dsniff - A tool for SSH and SSL MITM attacks
- Cain - A Windows GUI tool which can perform MITM attacks, along with sniffing and ARP poisoning
- Ettercap - A tool for LAN based MITM attacks
- Karma - A tool that uses 802.11 Evil Twin attacks to perform MITM attacks
- AirJack - A tool that demonstrates 802.11 based MITM attacks
- SSLStrip A tool for SSL based MITM attacks.
- SSLSniff A tool for SSL based MITM attacks. Originally was made to exploit a flaw[6] in Internet Explorer.
- Mallory - A transparent TCP and UDP MiTMing proxy. Extensible to MiTM SSL, SSH, and many other protocols.
- wsniff - A tool for 802.11 HTTP/HTTPS based MITM attacks
- an additional card reader and a method to intercept key-presses on an Automated teller machine
See also
- Examples
- Aspidistra transmitter — A British radio transmitter used for World War II “intrusion” operations, an early man-in-the-middle attack.
- Babington Plot — The plot against Elizabeth I of England, where Walsingham intercepted the correspondence.
- Other attacks
- Man in the Browser — An attack by corrupting a web browser.
- Meet-in-the-middle attack — An attempt to break a two-stage encryption by finding a match between the results of the first stage and the results of the inverse of the second stage.
- Miss in the middle attack – An efficient technique in impossible differential cryptanalysis, i.e. cryptanalysis based on excluding certain behaviours in the encryption.
- Relay attack — An variant of a man-in-the-middle attack based on relaying an intercepted message verbatim to a valid but unintended recipient.
- Rootkit — subversion of an entire operating system, notably to hide keyloggers that intercept credentials
- Typhoid adware
- Background
- Computer security — The design of secure computer systems.
- Cryptanalysis — The art of deciphering encrypted messages with incomplete knowledge of how they were encrypted.
- Digital signature — A cryptographic guarantee of the authenticity of a text, usually the result of a calculation only the author is expected to be able to perform.
- Interlock Protocol — A specific protocol to circumvent a man-in-the-middle attack when the keys may have been compromised.
- Key management — How to manage cryptographic keys, including generation, exchange and storage.
- Key-agreement protocol — A protocol for establishing a key in which both parties can have confidence.
- Mutual authentication — How communicating parties establish confidence in one another's identities.
- Password-authenticated key agreement — A protocol for establishing a key using a password.
- Quantum cryptography — The use of quantum mechanics to provide security in cryptography (while older methods rely on one-way functions).
- Secure channel — A way of communicating resistant to interception and tampering.
References
- ^ "Network Forensic Analysis of SSL MITM Attacks". NETRESEC Network Security Blog. http://www.netresec.com/?page=Blog&month=2011-03&post=Network-Forensic-Analysis-of-SSL-MITM-Attacks. Retrieved March 27, 2011.
- ^ Leyden, John (2003-11-07). "Help! my Belkin router is spamming me". The Register. http://www.theregister.co.uk/2003/11/07/help_my_belkin_router/.
- ^ "Petmail Documentation: Steal People's Time To Solve CAPTCHA Challenges". http://petmail.lothar.com/design.html#auto35. Retrieved 2008-05-19.
- ^ "CAPTCHA Effectiveness". 2006-10-25. http://www.codinghorror.com/blog/archives/000712.html.
- ^ "PC stripper helps spam to spread". BBC News. 2007-10-30. http://news.bbc.co.uk/2/hi/technology/7067962.stm.
- ^ Goodin, Dan (October 1, 2009). "SSL spoof bug still haunts IE, Safari, Chrome; Thanks to Microsoft". The Register.co.uk. http://www.theregister.co.uk/2009/10/01/microsoft_crypto_ssl_bug/. Retrieved July 17, 2010.
External links
Categories:- Cryptographic attacks
Wikimedia Foundation. 2010.