- Digital watermarking
-
Digital watermarking is the process of embedding information into a digital signal which may be used to verify its authenticity or the identity of its owners, in the same manner as paper bearing a watermark for visible identification. In digital watermarking, the signal may be audio, pictures, or video. If the signal is copied, then the information also is carried in the copy. A signal may carry several different watermarks at the same time.
In visible digital watermarking, the information is visible in the picture or video. Typically, the information is text or a logo, which identifies the owner of the media. The image on the right has a visible watermark. When a television broadcaster adds its logo to the corner of transmitted video, this also is a visible watermark.
In invisible digital watermarking, information is added as digital data to audio, picture, or video, but it cannot be perceived as such (although it may be possible to detect that some amount of information is hidden in the signal). The watermark may be intended for widespread use and thus, is made easy to retrieve or, it may be a form of steganography, where a party communicates a secret message embedded in the digital signal. In either case, as in visible watermarking, the objective is to attach ownership or other descriptive information to the signal in a way that is difficult to remove. It also is possible to use hidden embedded information as a means of covert communication between individuals.
One application of watermarking is in copyright protection systems, which are intended to prevent or deter unauthorized copying of digital media. In this use, a copy device retrieves the watermark from the signal before making a copy; the device makes a decision whether to copy or not, depending on the contents of the watermark. Another application is in source tracing. A watermark is embedded into a digital signal at each point of distribution. If a copy of the work is found later, then the watermark may be retrieved from the copy and the source of the distribution is known. This technique reportedly has been used to detect the source of illegally copied movies.
Annotation of digital photographs with descriptive information is another application of invisible watermarking.
While some file formats for digital media may contain additional information called metadata, digital watermarking is distinctive in that the data is carried right in the signal.
Contents
Applications
Digital watermarking may be used for a wide range of applications, such as:
- Copyright protection
- Source tracking (different recipients get differently watermarked content)
- Broadcast monitoring (television news often contains watermarked video from international agencies)
- Covert communication
Digital watermarking life-cycle phases
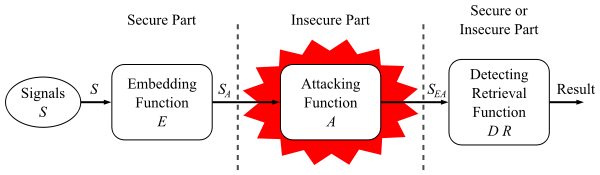
The information to be embedded in a signal is called a digital watermark, although in some contexts the phrase digital watermark means the difference between the watermarked signal and the cover signal. The signal where the watermark is to be embedded is called the host signal. A watermarking system is usually divided into three distinct steps, embedding, attack, and detection. In embedding, an algorithm accepts the host and the data to be embedded, and produces a watermarked signal.
Then the watermarked digital signal is transmitted or stored, usually transmitted to another person. If this person makes a modification, this is called an attack. While the modification may not be malicious, the term attack arises from copyright protection application, where pirates attempt to remove the digital watermark through modification. There are many possible modifications, for example, lossy compression of the data (in which resolution is diminished), cropping an image or video, or intentionally adding noise.
Detection (often called extraction) is an algorithm which is applied to the attacked signal to attempt to extract the watermark from it. If the signal was unmodified during transmission, then the watermark still is present and it may be extracted. In robust digital watermarking applications, the extraction algorithm should be able to produce the watermark correctly, even if the modifications were strong. In fragile digital watermarking, the extraction algorithm should fail if any change is made to the signal.
Classification
A digital watermark is called robust with respect to transformations if the embedded information may be detected reliably from the marked signal, even if degraded by any number of transformations. Typical image degradations are JPEG compression, rotation, cropping, additive noise, and quantization. For video content, temporal modifications and MPEG compression often are added to this list. A digital watermark is called imperceptible if the watermarked content is perceptually equivalent to the original, unwatermarked content.[1] In general, it is easy to create robust watermarks—or—imperceptible watermarks, but the creation of robust—and—imperceptible watermarks has proven to be quite challenging.[2] Robust imperceptible watermarks have been proposed as tool for the protection of digital content, for example as an embedded no-copy-allowed flag in professional video content.[3]
Digital watermarking techniques may be classified in several ways.
Robustness
A digital watermark is called fragile if it fails to be detectable after the slightest modifks, but as generalized barcodes.
A digital watermark is called semi-fragile if it resists benign transformations, but fails detection after malignant transformations. Semi-fragile watermarks commonly are used to detect malignant transformations.
A digital watermark is called robust if it resists a designated class of transformations. Robust watermarks may be used in copy protection applications to carry copy and no access control information.
Perceptibility
A digital watermark is called imperceptible if the original cover signal and the marked signal are (close to) perceptually indistinguishable.
A digital watermark is called perceptible if its presence in the marked signal is noticeable, but non-intrusive.
Capacity
The length of the embedded message determines two different main classes of digital watermarking schemes:
- The message is conceptually zero-bit long and the system is designed in order to detect the presence or the absence of the watermark in the marked object. This kind of watermarking scheme is usually referred to as zero-bit or presence watermarking schemes. Sometimes, this type of watermarking scheme is called 1-bit watermark, because a 1 denotes the presence (and a 0 the absence) of a watermark.
- The message is a n-bit-long stream (
 , with n = | m | ) or M = {0,1}n and is modulated in the watermark. These kinds of schemes usually are referred to as multiple-bit watermarking or non-zero-bit watermarking schemes.
, with n = | m | ) or M = {0,1}n and is modulated in the watermark. These kinds of schemes usually are referred to as multiple-bit watermarking or non-zero-bit watermarking schemes.
Embedding method
A digital watermarking method is referred to as spread-spectrum if the marked signal is obtained by an additive modification. Spread-spectrum watermarks are known to be modestly robust, but also to have a low information capacity due to host interference.
A digital watermarking method is said to be of quantization type if the marked signal is obtained by quantization. Quantization watermarks suffer from low robustness, but have a high information capacity due to rejection of host interference.
A digital watermarking method is referred to as amplitude modulation if the marked signal is embedded by additive modification which is similar to spread spectrum method, but is particularly embedded in the spatial domain.
Evaluation and benchmarking
The evaluation of digital watermarking schemes may provide detailed information for a watermark designer or for end-users, therefore, different evaluation strategies exist. Often used by a watermark designer is the evaluation of single properties to show, for example, an improvement. Mostly, end-users are not interested in detailed information. They want to know if a given digital watermarking algorithm may be used for their application scenario, and if so, which parameter sets seems to be the best.
Cameras
Epson and Kodak have produced cameras with security features such as the Epson PhotoPC 3000Z and the Kodak DC-290. Both cameras added irremovable features to the pictures which distorted the original image, making them unacceptable for some applications such as forensic evidence in court. According to Blythe and Fridrich, "[n]either camera can provide an undisputable proof of the image origin or its author".[4]
A secure digital camera (SDC) was proposed by Mohanty, et al. in 2003 and published in January 2004. This was not the first time this was proposed.[5] Blythe and Fridrich also have worked on SDC in 2004[4] for a digital camera that would use lossless watermarking to embed a biometric identifier together with a cryptographic hash.[6]
Reversible data hiding
Reversible data hiding is a technique which enables images to be authenticated and then restored to their original form by removing the digital watermark and replacing the image data that had been overwritten. This would make the images acceptable for legal purposes. The U.S. Army also is interested in this technique for authentication of reconnaissance images.[7]
Watermarking for relational databases
Digital watermarking for relational databases emerged as a candidate solution to provide copyright protection, tamper detection, traitor tracing, maintaining integrity of relational data. Many watermarking techniques have been proposed in the literature to address these purposes. A survey of the current state-of-the-art and a classification of the different techniques according to their intent, the way they express the watermark, the cover type, the granularity level, and their verifiability, can be found in
jucs.org.[8]See also
- Audio watermark detection
- Coded Anti-Piracy
- Copy attack
- EURion constellation
- Pattern Recognition (novel)
- Steganography
- Watermark (data file)
- Watermark detection
References
- ^ Khan, A. and Mirza, A. M. 2007. Genetic perceptual shaping: Utilizing cover image and conceivable attack information during watermark embedding. Inf. Fusion 8, 4 (Oct. 2007), 354-365
- ^ Ingemar J. Cox, Matthew L. Miller, Jeffrey A. Bloom, Jessica Fridrich and Ton Kalker, "Digital Watermarking and Steganography" (Second Edition), Morgan Kaufmann, 2008
- ^ Copy Protection Technical Working Group (CPTWG)
- ^ a b Paul Blythe and Jessica Fridrich, Secure Digital Camera, http://www.ws.binghamton.edu/fridrich/Research/DFRWSfinal.pdf
- ^ Saraju P. Mohanty, Nagarajan Ranganathan, and Ravi K. Namballa, VLSI Implementation of Visible Watermarking for a Secure Digital Still Camera Design, http://www.cse.unt.edu/~smohanty/research/ConfPapers/2004/MohantyVLSID2004Chip.pdf
- ^ Toshikazu Wada, Fay Huang (2009), Advances in Image and Video Technology, p. 340–341, ISBN 9783540929567, http://books.google.com/?id=zHGHCDLIg1oC&pg=PA340
- ^ Unretouched by human hand, The Economist, December 12th 2002, http://www.economist.com/sciencetechnology/tq/displayStory.cfm?story_id=E1_TQSGSPP
- ^ Raju Halder, Shantanu Pal, and Agostino Cortesi, Watermarking Techniques for Relational Databases: Survey, Classification and Comparison, The Journal of Universal Computer Science, vol 16(21), pp. 3164-3190, 2010.hell0, http://www.jucs.org/jucs_16_21/watermarking_techniques_for_relational/jucs_16_21_3164_3190_halder.pdf
Further reading
- ECRYPT report: Audio Benchmarking Tools and Steganalysis
- ECRYPT report: Watermarking Benchmarking
- Jana Dittmann, David Megias, Andreas Lang, Jordi Herrera-Joancomarti; Theoretical framework for a practical evaluation and comparison of audio watermarking schemes in the triangle of robustness, transparency and capacity; In: Transaction on Data Hiding and Multimedia Security I; Springer LNCS 4300; Editor Yun Q. Shi; pp. 1-40; ISBN 978-3-540-49071-5,2006 PDF
- M. V. Smirnov. Holographic approach to embedding hidden watermarks in a photographic image //Journal of Optical Technology, Vol. 72, Issue 6, pp. 464-468
External links
- Digital Watermarking Alliance
- Digital Watermarking & Data Hiding research papers at forensics.nl
- Directory of Books, Journals & Conferences on Digital Watermarking and Digital Watermarking Assessment Tools
- Information hiding homepage by Fabien Petitcolas
- Comparison of watermarking methods
- Robust Mesh Watermarking
- PhotoWaterMark technology: Holographic approach
- Open Platform for testing digital watermarking systems
- Watermarking Lecture
- Watermarking on stone
Categories:- Authentication methods
- Watermarking
- Digital photography
- Digital watermarking
Wikimedia Foundation. 2010.